KTrust Reinvents Kubernetes Security with Real-Time Attack SimulationsPublished on CloudWireHub
- Rahul Patil
- Feb 25, 2025
- 2 min read
Introduction
In an era where Kubernetes has become the backbone of cloud-native deployments, securing it has never been more critical. KTrust, a Tel Aviv-based security startup, is changing the Kubernetes security game with a proactive, attack-based approach. Rather than passively scanning for known vulnerabilities, KTrust deploys real-world hacking simulations to identify genuine threat vectors. This dynamic methodology provides security teams with actionable insights, significantly reducing the noise that traditional scanners generate.
What Sets KTrust Apart?
Most Kubernetes security tools rely on static analysis or configuration scanning, resulting in an overwhelming number of potential vulnerabilities. However, KTrust acts like a "red team in a box," simulating cyberattacks within a sandboxed version of a customer’s Kubernetes environment. This allows DevSecOps teams to prioritize actual, validated attack paths over theoretical risks.
Gartner has categorized this approach under "Continuous Threat Exposure Management" (CTEM), emphasizing its real-world relevance.
"By doing this, we find actual attack paths to exploit and you don’t get a list of hundreds of items that are not connected," explains KTrust CEO Nadav Toledo. "We show the DevSecOps the validated exploits — and it’s true validation because it was a real attack."

A Team Built for the Mission
KTrust's leadership is stacked with industry veterans:
Nadav Toledo (CEO): Former colonel in the IDF’s elite Unit 8200 with 25 years of experience.
Nadav Aharon-Nov (CTO): Ex-CTO of cyberintelligence firm R-MOR.
Sigalit Shavit (COO): Former Global CIO at CyberArk.
Snir Maizlik (CBO): Business strategist with experience across global markets.
This diverse mix of military-grade security, enterprise IT, and business acumen positions KTrust to tackle both the technical and commercial challenges of scaling a next-gen security platform.
How the Technology Works
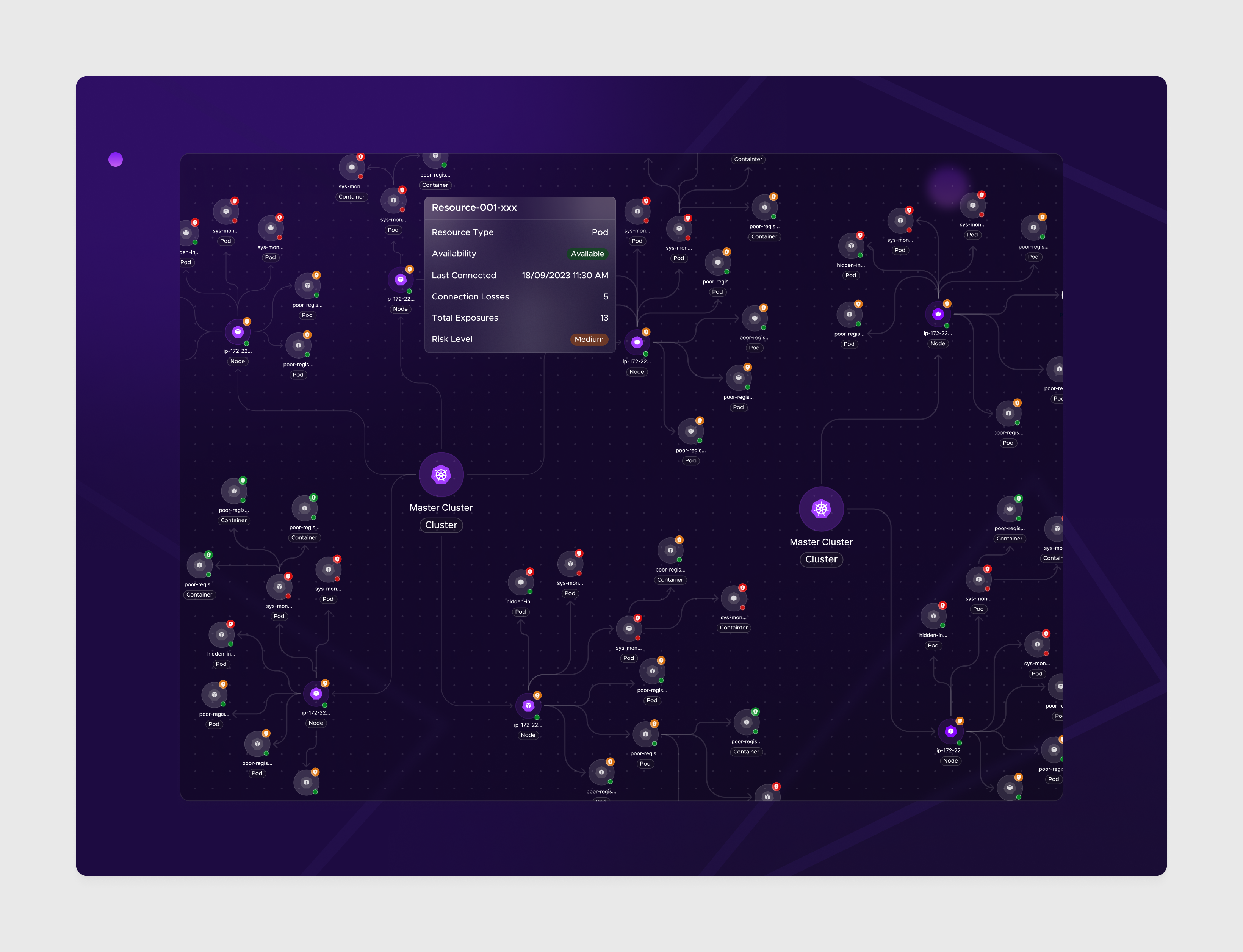
KTrust’s agent-based system starts by duplicating a company’s Kubernetes infrastructure into a secure sandbox. It then simulates attacks on this environment using algorithms that mimic real-world hacker behavior.
In one client case study, a traditional passive scanner flagged over 500 potential vulnerabilities. KTrust's system distilled these into just 12 valid, exploitable attack paths.
Once vulnerabilities are found, the platform provides:
Visualizations of the attack paths
Manual and automated mitigation recommendations
Continuous retesting after changes
Additionally, KTrust maintains a dedicated research team focused on discovering new Kubernetes vulnerabilities. The company has already submitted several CVEs for Kubernetes and Argo CD, underscoring its commitment to advancing cloud security at large.
Funding and Market Opportunity
KTrust recently emerged from stealth mode with a $5.4 million seed funding round led by Awz Ventures.
"Our investment in KTrust signifies our confidence in their distinctive Kubernetes security solution, meeting a critical market demand," said Yaron Ashkenazi, managing partner at Awz Ventures. "KTrust will scale to empower DevSecOps globally in ensuring the secure deployment of their Kubernetes-based applications."
With cloud-native adoption continuing to grow, and Kubernetes becoming a de facto standard, the market for advanced Kubernetes security solutions is expected to surge.
Kubernetes Security with Real-Time Attack
Conclusion
KTrust is delivering a much-needed shift in how Kubernetes security is approached. By actively simulating attacks and exposing real threats, it offers teams a smarter, faster, and more effective way to secure their cloud-native applications. In a world flooded with security tools, KTrust’s approach isn’t just different — it’s necessary.
Stay tuned to CloudWireHub for more updates on emerging Kubernetes security technologies and DevSecOps trends.


Comments